CH1: Intro to Digital Forensics
Chapter Overview
This foundational chapter distinguishes Digital Forensics from traditional IT operations and Incident Response. While the technical tools may look similar, the goals, and the stakes, are vastly different. We will explore the "Golden Rules" that guide our every move, rooted in the scientific concept of Locard's Exchange Principle.
Technical skill alone is not enough. A forensic investigator operates at the intersection of technology and the law. Therefore, this chapter also establishes the crucial legal frameworks, including the 4th Amendment and the concept of Reasonable Expectation of Privacy, which determine when and how digital evidence can be seized. Finally, we will define the ethical responsibilities of an expert witness, ensuring that you understand the weight of your role in the pursuit of justice.
Learning Objectives
By the end of this chapter, you will be able to:
- Define Digital Forensics and distinguish it from IT Operations and Incident Response.
- Categorize Digital Evidence into Real, Documentary, Testimonial, and Demonstrative types.
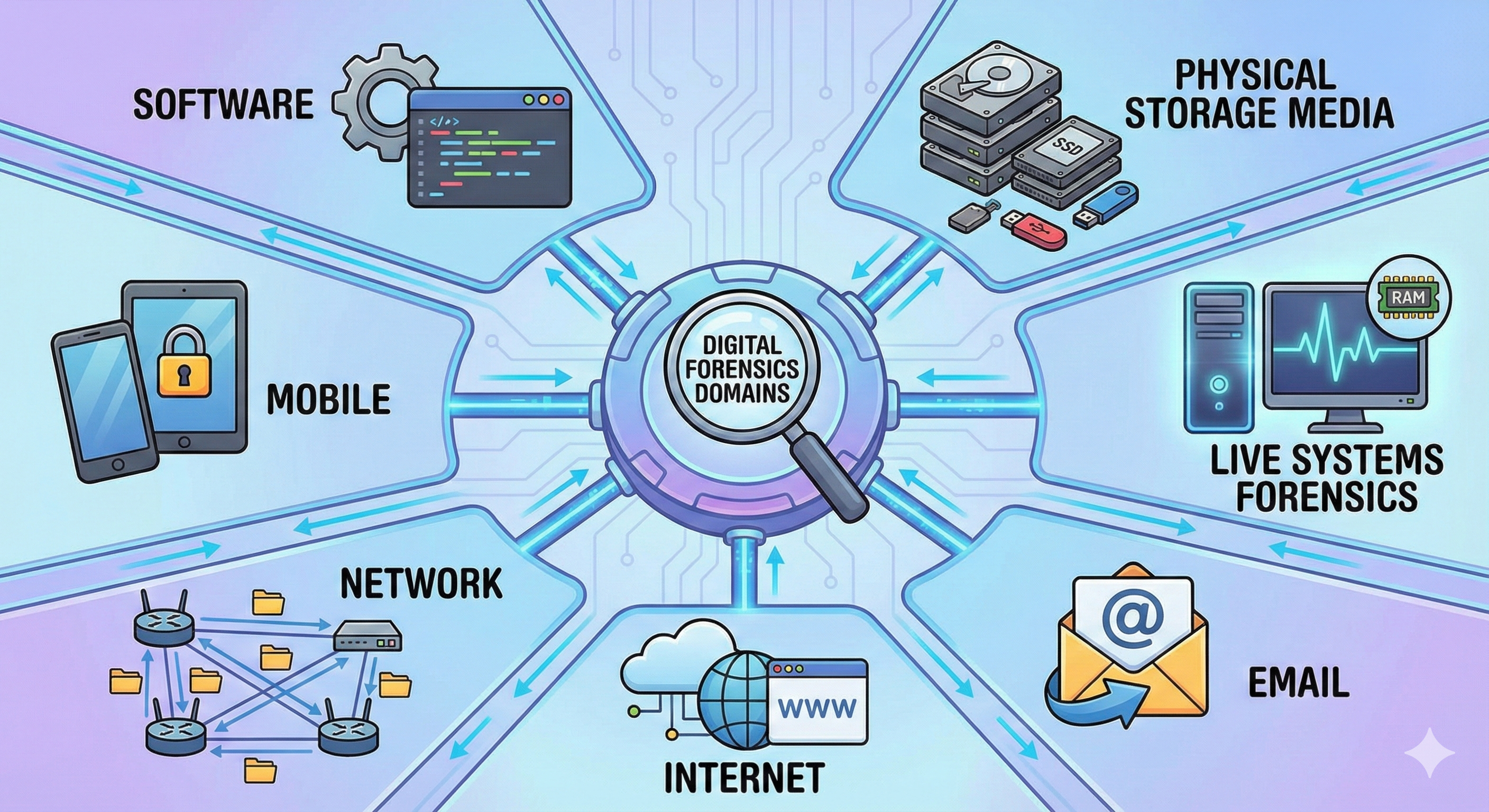
- Identify the domains of forensic analysis, including Physical Media, Mobile, and Network forensics.
- Apply "Locard's Exchange Principle" to digital crime scenes to understand why evidence handling is critical.
- Explain the importance of NIST SP 800-86 and SANS frameworks in establishing legal defensibility.
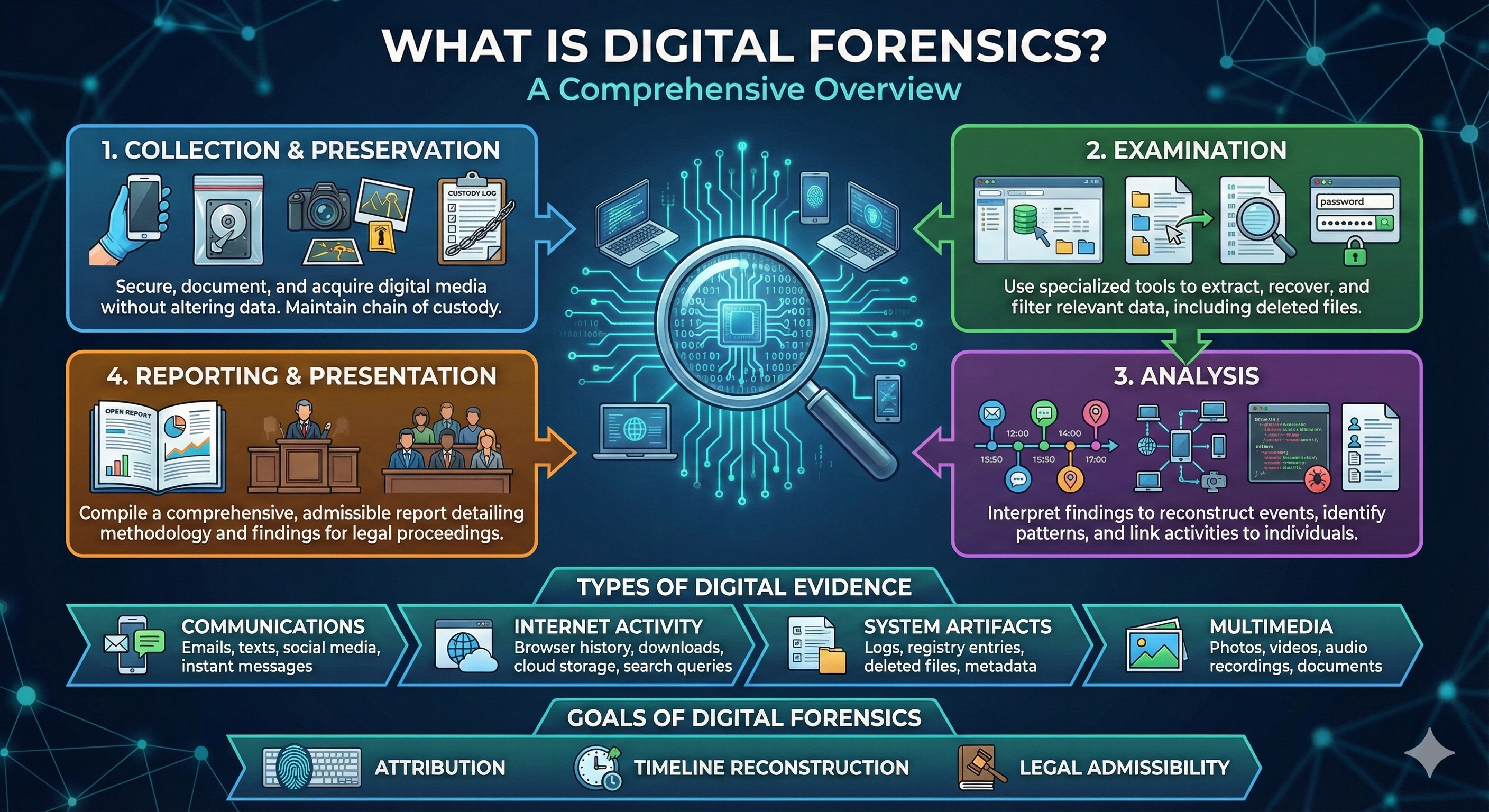
- Analyze the Digital Forensics Lifecycle, from Identification to Presentation.
- Evaluate legal authority under the 4th Amendment, including Search Warrants, Consent, and Exigent Circumstances.
- Apply the "Daubert Standard" to determine if a forensic tool or technique is admissible in court.
- Uphold the ethical duties of an Expert Witness, specifically regarding the Brady Rule and bias confirmation.
1.1 Introduction to the Discipline
Digital forensics is often misunderstood, frequently glamorized by television procedurals where complex encryptions are broken in seconds and evidence is found with a single keystroke. The actual practice of digital forensics is a careful, deliberate science. It functions as the bridge between technology and the law. The work goes beyond finding "bad stuff" on a computer; it centers on preserving the narrative of a crime or incident in a way that is indisputable in a court of law.
This course, CFS137, begins with Phase 1: Foundations, Preservation, and Documentation. Before touching a piece of evidence, an investigator must understand the "Golden Rules" of forensics and the legal framework that governs their actions. A failure in technical skill can often be fixed; a failure in legal authority or ethics typically results in the total inadmissibility of evidence.
1.2 Defining Digital Forensics
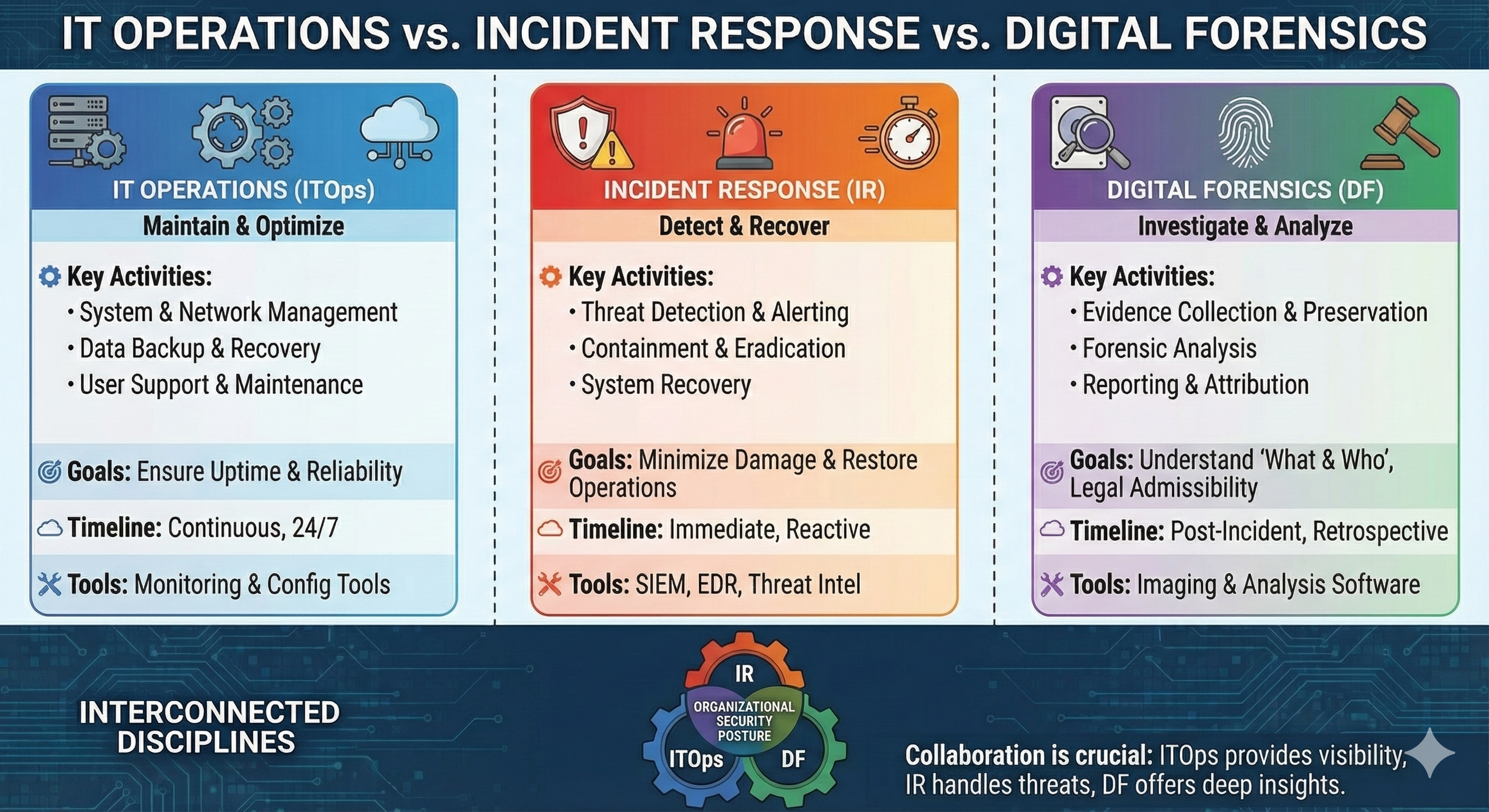
To act as a forensic examiner, one must understand how this role differs from other technology disciplines. While the skill sets overlap, the goals are fundamentally different.
Operations vs. Incident Response vs. Forensics
In a professional environment, three distinct groups may touch a computer system, but they operate under different mandates:
-
IT Operations (System Administration):
- Goal: Availability and Uptime.
- Mindset: "Fix it now."
- Action: If a server is running slowly due to a rogue process, an IT administrator kills the process and reboots the server.
- Forensic Consequence: The volatile memory (RAM) is lost, and the history of the rogue process is destroyed.
-
Incident Response (IR):
- Goal: Containment and Recovery.
- Mindset: "Stop the bleeding."
- Action: If a hacker is actively exfiltrating data, the IR team isolates the machine from the network to stop the theft.
- Forensic Consequence: While necessary, this alters the state of the network connections and may trigger "dead man switches" in malware.
-
Digital Forensics:
- Goal: Attribution and Legal Proof.
- Mindset: "Preserve and Analyze."
- Action: The forensic examiner prioritizes the preservation of the data in its current state to answer the questions: Who did this? How did they do it? When did it happen?
1.3 The Nature of Evidence
Before we can analyze data, we must define what we are looking for.
What is Digital Evidence?
Digital evidence is any information of probative value that is stored or transmitted in a binary form. Unlike a physical gun or a bag of narcotics, digital evidence is latent; it cannot be seen or touched directly. It requires hardware and software tools to make it visible and intelligible to humans.
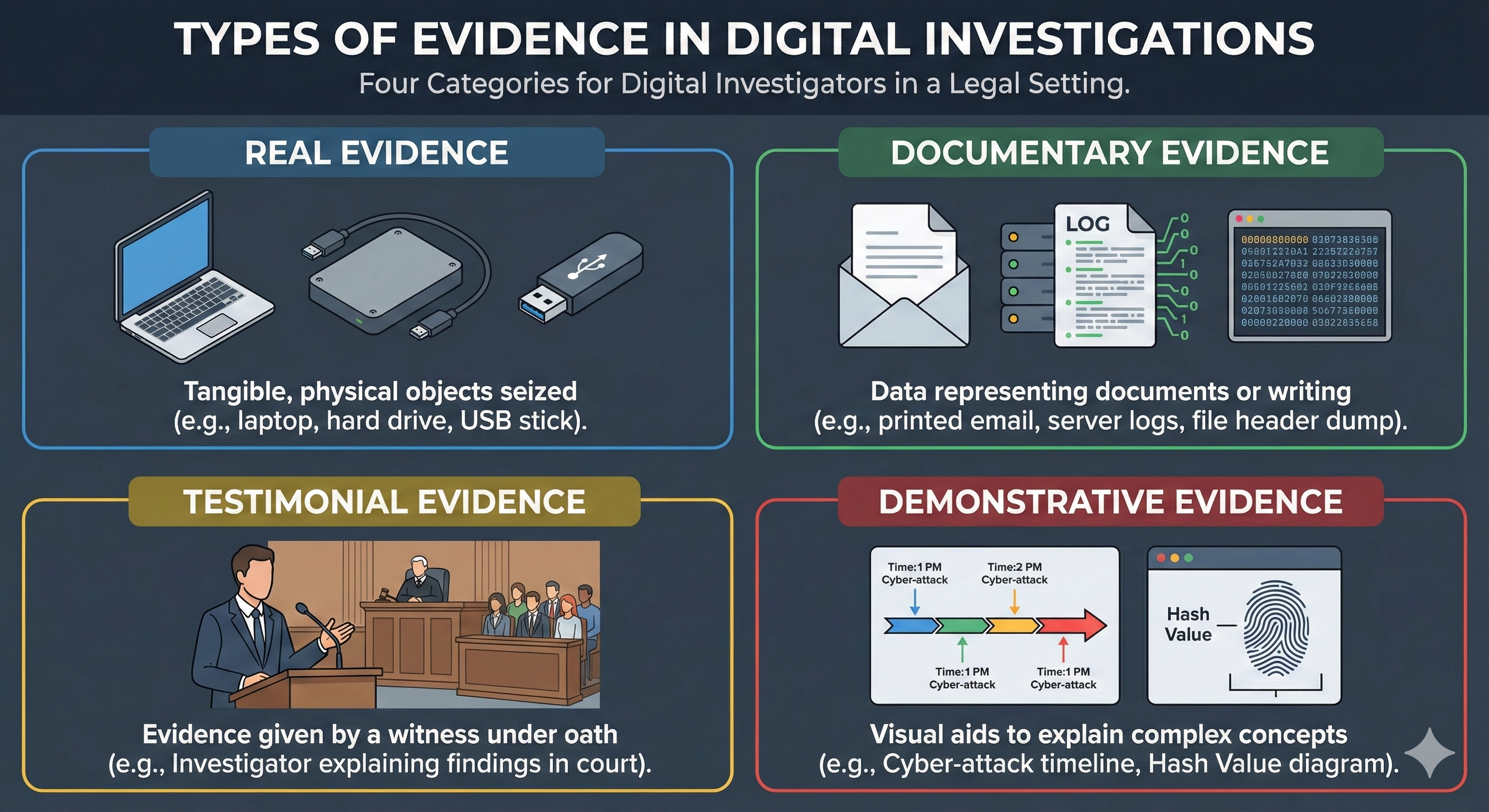
Types of Evidence
In a legal setting, evidence generally falls into four categories. As a digital investigator, you will likely deal with all four:
- Real Evidence: This is the tangible, physical object. In our field, the "Real" evidence is the physical laptop, the hard drive, or the USB stick seized from the suspect.
- Documentary Evidence: This is data representing a document or writing. A printed email, a server log file, or a hex dump of a file header are examples of documentary evidence.
- Testimonial Evidence: This is the evidence given by a witness under oath. When you, as the investigator, take the stand to explain your findings to a judge or jury, you are providing testimonial evidence.
- Demonstrative Evidence: These are visual aids used to help the jury understand complex concepts. A chart showing the timeline of a cyber-attack or a diagram explaining how a "Hash Value" acts as a digital fingerprint are examples of demonstrative evidence.
1.4 Domains of Digital Forensics
Digital forensics is a broad umbrella. While the principles of preservation remain the same, the specific techniques vary depending on where the evidence lives.
- Physical Storage Media Forensics: The traditional analysis of powered-off systems, including hard drives (HDD), Solid State Drives (SSD), and USB devices. This involves file systems (NTFS), deleted data recovery, and registry analysis.
- Live System Forensics: Analyzing a computer while it is still running. This focuses on Volatile Memory (RAM) to capture encryption keys, running processes, and active network connections that vanish when the power is cut.
- Email Forensics: Investigating the source and content of emails. This includes analyzing header information (X-Originating-IP), tracing the path of the message, and identifying phishing attacks.
- Internet/Browser Forensics: Reconstructing a user's web activity. This involves analyzing browser history, cookies, cache, and download logs to prove a suspect visited a specific site or downloaded illegal material.
- Mobile Forensics: The extraction of data from iOS and Android devices. This is distinct because of the "walled garden" security models, sandbox environments, and heavy reliance on cloud synchronization.
- Network Forensics: Analyzing traffic logs, firewall logs, and packet captures to reconstruct how an attacker moved through a network.
- Software Forensics: This often involves malware analysis and reverse engineering to understand the purpose and function of a malicious program or script.
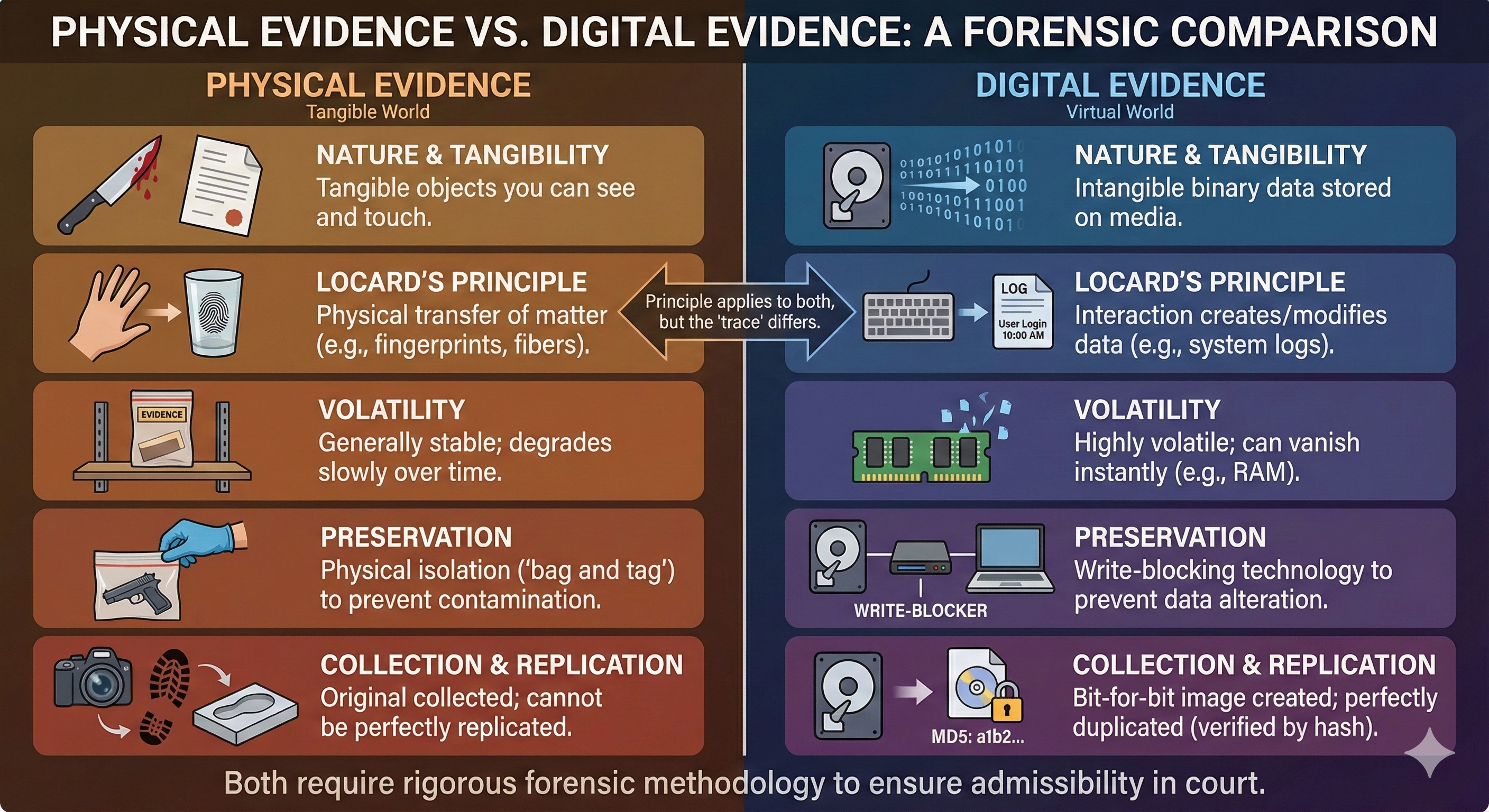
1.5 The Scientific Foundation: Locard's Exchange Principle
The foundational principle of forensic science, both physical and digital, is Locard's Exchange Principle. Edmond Locard, a French criminologist often referred to as the "Sherlock Holmes of France," established this theory in the early 20th century.
The Core Concept
Locard's principle is summarized by the phrase: "Every contact leaves a trace."
In the physical world, this is intuitive. If a burglar enters a room, they leave something behind (fingerprints, muddy footprints, hair) and they take something with them (carpet fibers on their shoes, dust on their clothes). This mutual exchange proves the interaction occurred.
Application to Digital Environments
In the digital realm, this principle is absolute and unforgiving. It is virtually impossible to interact with a computer system without altering it. The "exchange" happens at the binary level:
-
The Exchange (Investigator Side): When you touch a keyboard or plug in a device, you are introducing new data to the system.
- Timestamps: Simply viewing a file's properties can update the "Last Accessed" timestamp, destroying the original timeline of when the suspect last opened it.
- Registry Hives: Plugging in your forensic USB drive causes the Windows Operating System to mount the device, creating entries in the Registry (specifically the
USBSTORkey) that record your device's presence. - Log Files: Booting a system generates event logs (System and Security logs) that record the startup process, overwriting older logs due to size limits.
-
The Exchange (Suspect Side): Just as a burglar takes dust, a digital intruder takes data. Even if they "delete" the files they stole, the act of copying them to an external drive leaves artifacts (Link files, Shellbags, and Jumplists) that prove the data was there.
The "Butterfly Effect" of Forensics
For a student new to this field, this principle serves as a warning. In IT support, if you make a mistake, you can usually "Undo" or restore from backup. In forensics, you cannot undo a footprint.
If an investigator turns on a suspect's computer to "quickly check" if the evidence is there, they have violated Locard's principle by contaminating the crime scene. In court, a defense attorney can argue that the "trace" found on the computer (like a modified date) was placed there by the investigator, not the suspect. This effectively destroys the integrity of the evidence.
Golden Rule: Because of Locard's Exchange Principle, we never work on the original evidence if it can be avoided. We create a forensic copy (image) and analyze the copy, leaving the original untouched.
1.6 The Digital Forensics Lifecycle (NIST & ISO)
In the early days of computer crime, investigations were the "Wild West." Techniques varied from person to person, and evidence was frequently thrown out of court because the methods were unproven or sloppy.
To mitigate these risks, digital forensics professionals rely on standardized lifecycles. These frameworks provide a roadmap for the investigation, ensuring consistency and repeatability. If another expert were to take the same evidence and follow your steps, they should arrive at the same conclusion. This concept is known as reproducibility, and it is a foundational requirement of forensic science.
While various organizations have proposed different models, two stand out as the gold standards for modern investigators: the NIST SP 800-86 (popular in the United States and federal sectors) and the international standard ISO/IEC 27037 (recognized globally).
Why These Frameworks?
- NIST (National Institute of Standards and Technology): This is a U.S. government agency. Their publication, NIST SP 800-86 (Guide to Integrating Forensic Techniques into Incident Response), is considered the standard for digital forensics. When you testify in court, being able to say, "I followed the procedure established by the National Institute of Standards and Technology," provides significant credibility. It satisfies the requirement for standardized, repeatable methods.
- International Organization for Standardization (ISO): A globally recognized non-governmental body that develops voluntary, consensus-based international standards to ensure quality, safety, and efficiency across almost every industry. In the context of digital forensics, ISO provides the critical "rulebook" that allows investigators from different countries and jurisdictions to operate under a unified framework. Specifically, standards like ISO/IEC 27037 establish rigorous guidelines for the identification, collection, acquisition, and preservation of digital evidence, ensuring that the handling of data is consistent and scientifically valid.
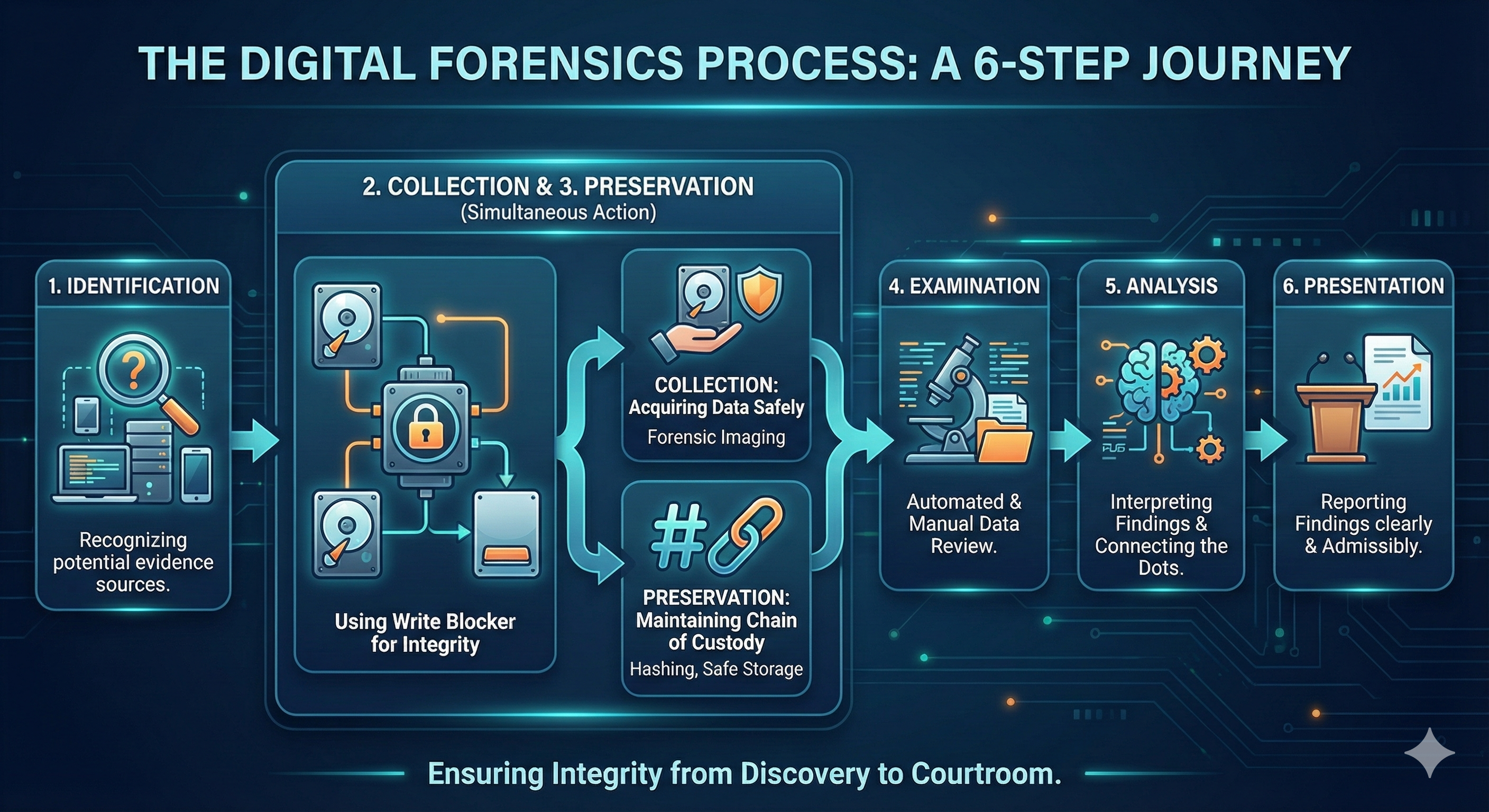
The Forensic Phases
The lifecycle is generally divided into six critical phases which is a synthesis of both NIST and ISO standards:
-
Identification (Scope):
- Before touching a keyboard, you must define what you are looking for. Is it a single laptop? A server? A smartphone?
- This phase involves legal authorization. Do you have a warrant? What does the warrant allow you to search?
-
Collection (Acquisition):
- This involves the physical seizure and active acquisition of the digital data. We must ensure the act of collecting the data does not alter it. You are technically "Preserving (Step 3)" the data as you collect it.
- We use Write Blockers (hardware bridges) during this phase. These devices physically allow data to flow out of the suspect drive but stop any data from flowing in, preventing contamination (Locard's Principle).
- We do not just copy files (Ctrl+C, Ctrl+V). We perform Forensic Imaging. This creates a bit-for-bit clone of the drive, capturing every 1 and 0, including the empty space (Unallocated Space) where deleted evidence often hides.
-
Preservation (Integrity):
- Once the data is collected, we must "freeze" the evidence and guarantee it remains unchanged until trial.
- This relies on Hashing (creating digital fingerprints like MD5 or SHA256). We hash the evidence immediately after collection; if a single bit changes later, the hash will change, alerting us to tampering.
- We also maintain a strict Chain of Custody, which is a chronological paper trail documenting exactly who handled the evidence, when, and where it was stored.
-
Examination (Filtering):
- A modern hard drive has millions of files. Most are part of the Operating System (Windows) and are irrelevant to the crime.
- In this phase, we use automated tools to filter out known good files (like
notepad.exe) so we can focus on the user's documents, emails, and downloads.
-
Analysis (Correlation):
- This is where "Data" becomes "Evidence."
- You might find a file, but Analysis asks: How did it get there?
- You correlate artifacts: "The user downloaded this file at 4:00 PM (Browser History), saved it to the Desktop (File System), and opened it at 4:05 PM (LNK File)." This builds the narrative.
-
Presentation (Reporting):
- The most technical analysis is useless if a jury cannot understand it.
- This phase involves writing a clear, non-technical report that explains your findings, your methodology, and your conclusion. It must be defensible under cross-examination.
1.7 Legal Authority: The Framework of Search
In the United States, digital forensics is heavily constrained by the 4th Amendment to the Constitution, which protects citizens against unreasonable searches and seizures.
The 4th Amendment: "The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated..."
Reasonable Expectation of Privacy (REP)
The threshold for whether a search is legal often hinges on whether the individual had a "Reasonable Expectation of Privacy" (REP). This standard was established in the landmark Supreme Court case Katz v. United States (1967).
- The Case: Charles Katz used a public phone booth to transmit illegal gambling wagers. The FBI attached a listening device to the outside of the booth.
- The Ruling: The Court ruled that the 4th Amendment protects people, not places. Even in a public phone booth, Katz had an expectation that his conversation would remain private when he closed the door.
- Digital Application: A user generally has REP on their personal, password-protected home computer. However, an employee may not have REP on a work computer if they signed an Acceptable Use Policy (AUP) stating that the company monitors activity.
Modes of Authority
To bypass REP and legally search a device, an investigator generally needs one of three things:
- Search Warrants: This is the gold standard for Law Enforcement. A warrant is a legal order signed by a judge authorizing the search. It requires Probable Cause and a specific Scope (what can be searched).
- Consent: A person can voluntarily waive their 4th Amendment rights. However, consent can be revoked at any time, and the person giving consent must have the authority to do so (e.g., a roommate cannot consent to search your password-protected laptop).
- Exigent Circumstances: This applies when there is an immediate threat to life or a risk of evidence destruction. Police may seize a device without a warrant to stop a hacker from wiping it, but usually need a warrant to subsequently search it.
The Plain View Doctrine
What happens if an investigator searching for one crime finds evidence of another? This is governed by the Plain View Doctrine.
-
The Rule: An investigator can seize evidence of a crime without a warrant if:
- The officer is lawfully present in the place where the evidence is found.
- The incriminating nature of the evidence is immediately apparent.
- The officer has a lawful right of access to the object.
-
Digital Example: An investigator has a warrant to search a hard drive for "Financial Spreadsheets." While opening a folder to look for them, they see a thumbnail image that is clearly child exploitation material (CEM). Because they were legally looking in that folder for spreadsheets, the CEM is in "Plain View."
Note
Plain view issues in digital searches can be contested; investigators often pause and seek additional legal guidance or a supplemental warrant when encountering evidence outside the warrant's scope.
1.8 Admissibility: The Daubert Standard
Collecting evidence legally is not enough; the methods used to analyze it must be scientifically valid. This is governed by the Daubert Standard (Daubert v. Merrell Dow Pharmaceuticals).
In federal courts and many state courts, the judge acts as a "Gatekeeper" to prevent "junk science" from entering the courtroom. For a forensic tool or technique to be admissible, the judge will assess it against these criteria:
- Testing: Has the technique or tool been tested?
- Peer Review: Has it been subjected to peer review and publication?
- Error Rate: Is the known or potential error rate defined?
- Standards: Do standards controlling the technique's operation exist?
- General Acceptance: Is the method generally accepted within the relevant scientific community?
Why this matters now: Even in Week 1, you must choose tools that meet these standards. If you use an obscure, untested beta script to analyze evidence, your entire testimony could be disqualified under Daubert months later.
1.9 Ethics and the Expert Witness
A digital forensic examiner holds significant authority. Access to a subject's entire digital life, the ability to reconstruct timelines, and the credibility of expert testimony all demand a strict ethical duty.
The Brady Rule
In criminal cases, the prosecution (and by extension, the forensic examiner working for the police) has a constitutional duty to disclose exculpatory evidence to the defense. This is known as the Brady Rule (Brady v. Maryland).
- Exculpatory Evidence: Evidence that might show the defendant is innocent.
- Scenario: You are investigating a suspect for sending a threatening email at 5:00 PM. You find the email, but you also find a GPS log on their phone showing they were driving (and not near a computer) at 5:00 PM. You must report the GPS log. Hiding it is a violation of due process.
Confirmation Bias
Examiners must guard against bias confirmation, the tendency to look only for evidence that supports the theory of guilt while ignoring evidence that contradicts it. Your job is not to convict; your job is to report the truth.
The Duty to the Court
Whether you are hired by the prosecution, the defense, or a private corporation, your primary duty as an Expert Witness is to the Court. You are an interpreter of technical facts, not a "hired gun" paid to say what the client wants.
1.10 Test Your Understanding

1.11 Chapter Summary
Digital Forensics is a discipline built on precision. Unlike IT operations, which prioritize speed, forensics prioritizes the preservation and accurate attribution of data. We operate under the constant reality of Locard's Exchange Principle, knowing that every interaction with a digital device alters it.
To manage this, we utilize the Digital Forensics Lifecycle (Identification, Preservation, Collection, Examination, Analysis, Presentation) rooted in NIST and SANS frameworks. This technical workflow must be executed within the bounds of the legal system, specifically the 4th Amendment and the concept of Reasonable Expectation of Privacy (REP).
We deal with various forms of evidence, Real, Documentary, Testimonial, and Demonstrative, and must ensure our methods meet the Daubert Standard for admissibility. Finally, the forensic examiner acts as a neutral seeker of truth, adhering to ethical mandates like the Brady Rule to provide a complete picture to the court.